#1 Full-Service Cybersecurity Agency
The Cybersecurity Agency You Wish You’d Hired First
We assess, build, and manage security frameworks that protect your business from real threats. From penetration testing to 24/7 monitoring and incident response, we keep your systems locked down and your data safe.
Cybersecurity Services That Leave No Vulnerability Unchecked

Assess your threat landscape and build a security strategy aligned with compliance and risk tolerance.
Strategy & Planning
What we do:
Deploy firewalls, SIEM, endpoint protection, and zero-trust frameworks tailored to your stack.
Implementation
What we do:

Unify security tools across cloud, network, and endpoint layers into a single pane of glass.
Integration
What we do:

Automate threat detection, incident response, and compliance reporting to stay ahead of risks.
Automation
What we do:
Transition security infrastructure to new platforms without gaps in coverage or compliance.
Migration
What we do:

24/7 monitoring, threat response, and continuous compliance management handled by our team.
Managed Services
What we do:
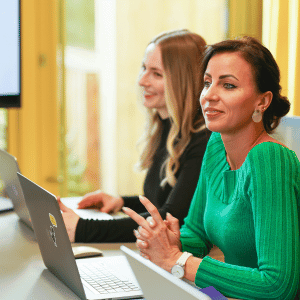
Why Businesses Choose SEC360
200+ Global Clients Served
Organizations worldwide trust our cybersecurity consultants to assess, design, and harden their security posture, protecting critical assets, ensuring compliance, and reducing risk across every layer.
15+ Platform Certifications
Our team holds certifications across CrowdStrike, Palo Alto, Fortinet, Splunk, SentinelOne, and more, delivering deep platform expertise so your defenses are configured, tested, and audit-ready.
100% Vendor-Neutral Guidance
Our security recommendations are driven by your risk profile, not vendor incentives. Every tool and framework we suggest is selected based on your threat landscape, compliance obligations, and infrastructure needs.
12+ Industry Verticals Served
From finance and healthcare to government, energy, and SaaS, we understand the regulatory frameworks, threat profiles, and data protection standards that define security in your specific industry.
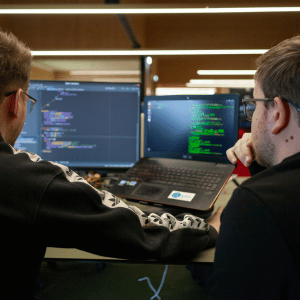
Your Security Transformation in 6 Steps
Step 1
We assess your threat landscape, existing security controls, and compliance posture to identify vulnerabilities and build a clear picture of your current risk.
Step 2
We develop a security roadmap covering architecture design, tool selection, policy frameworks, and phases, all aligned to your risk tolerance and compliance needs.
Step 3
We design your security architecture and configure firewalls, SIEM, endpoint protection, and access controls, building layered defenses tailored to your stack.
Step 4
We integrate security tools across cloud, network, and endpoint layers, connecting identity providers, log sources, and threat intel feeds into one unified view.
Step 5
Every rule, policy, and detection workflow is tested through simulated attacks and penetration testing. Your team receives incident response training before launch.
Step 6
Post-launch, we provide around-the-clock monitoring, threat hunting, compliance reporting, and tuning so your security posture strengthens as threats evolve.
Common Security Challenges We Help Solve
Blind Spots
You can’t protect what you can’t see, and gaps in visibility create real exposure. We map your entire attack surface and deploy monitoring that covers every layer of your stack.
Alert Fatigue
Your team is drowning in notifications with no way to prioritize real threats quickly. We tune detection rules and build response playbooks so only critical alerts reach your team fast.
Compliance Burden
Meeting regulatory requirements across frameworks takes too much time and manual effort. We automate compliance reporting and policy enforcement so you stay audit-ready.
Slow Response
When incidents happen, your team scrambles because there’s no structured playbook in place. We design and test incident response workflows so your team reacts fast and with confidence.
Make Your Security Smarter with AI
AI Threat Detection
Detect advanced threats in real time using AI that analyzes network behavior, user activity, and known attack patterns across your stack.
Smart Incident Triage
Let AI prioritize security alerts by severity and context automatically, so your team focuses on real threats instead of chasing noise.
Predictive Risk Scoring
Use AI to assess and score your organization’s risk exposure continuously, surfacing vulnerabilities before they become breaches or incidents.
Automated Policy Enforcement
Apply security policies consistently across endpoints, cloud, and network layers using AI that detects drift and corrects it in real time.